I recently decided to give Altibox and their 6rd implementation another go — searching the interwebs I stumbled upon a Norwegian forum post that read (translation by me):
Altibox offers native dual-stack IPv6 if your home central is in bridge mode. You get a /56 prefix though DHCPv6-PD (prefix delegation) and can split it into multiple /64 networks. (…) — sveinse
WHAT!? Really? They offer native dual-stack IPv6 with DHCPv6-PD? Let’s test it! 🥳
Table of contents
EdgeRouter configuration changes
I have the Altibox fiber plugged directly into my EdgeRouter 4.
There isn’t a lot of IPv6 stuff in the GUI, so you’ll have to work with the CLI or the config tree.
Interfaces
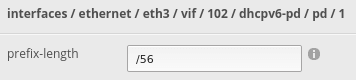
The first thing I did was configure DHCPv6-PD on my Altibox WAN interface. Under dhcpv6-pd I added a PD number of 1; here I set the prefix length to /56.
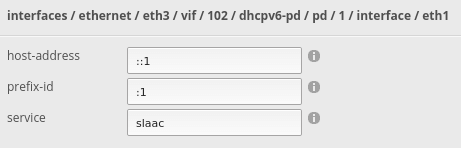
Next I added the eth1 interface, my LAN, and set host-address to ::1, prefix-id to :1, and service to slaac.
This tells the EdgeRouter to give out IPv6 addresses on the eth1 interface — using the SLAAC service and a prefix of :1. The router itself will get address ::1.
Also remember to set your IPv6 firewalls; WANv6_IN and WANv6_LOCAL.
interfaces {
ethernet eth3 {
duplex auto
mac xx:xx:xx:xx:xx:xx
speed auto
vif 102 {
address dhcp
dhcpv6-pd {
pd 1 {
interface eth1 {
host-address ::1
prefix-id :1
service slaac
}
prefix-length /56
}
rapid-commit enable
}
firewall {
in {
ipv6-name WANv6_IN
name WAN_IN
}
local {
ipv6-name WANv6_LOCAL
name WAN_LOCAL
}
}
}
}
}
Firewall
It’s important to keep in mind that dual-stack is exactly that; dual stack. You need a complete set of firewall rules for both IPv4 and IPv6. I made sure to have WANv6_IN (from WAN to inside) and WANv6_LOCAL (from WAN to router).
Some of these rules already existed on the EdgeRouter, I did add a rule to allow IPv6 ICMP to devices inside the network. This is required for IPv6 to function properly.
You won’t find these rules in the GUI either, so you’ll need to use the CLI or config tree.
For maximum security you could only allow the ICMP types needed, but I haven’t looked into that (yet). Here is a YouTube video on IPv6 security.
firewall {
ipv6-name WANv6_IN {
default-action drop
description "WAN inbound traffic forwarded to LAN"
enable-default-log
rule 10 {
action accept
description "Allow established/related sessions"
state {
established enable
related enable
}
}
rule 20 {
action drop
description "Drop invalid state"
state {
invalid enable
}
}
rule 30 {
action accept
description "Allow IPv6 icmp"
protocol ipv6-icmp
}
}
ipv6-name WANv6_LOCAL {
default-action drop
description "WAN inbound traffic to the router"
enable-default-log
rule 10 {
action accept
description "Allow established/related sessions"
state {
established enable
related enable
}
}
rule 20 {
action drop
description "Drop invalid state"
state {
invalid enable
}
}
rule 30 {
action accept
description "Allow IPv6 icmp"
protocol ipv6-icmp
}
rule 40 {
action accept
description "allow dhcpv6"
destination {
port 546
}
protocol udp
source {
port 547
}
}
}
ipv6-receive-redirects disable
ipv6-src-route disable
}
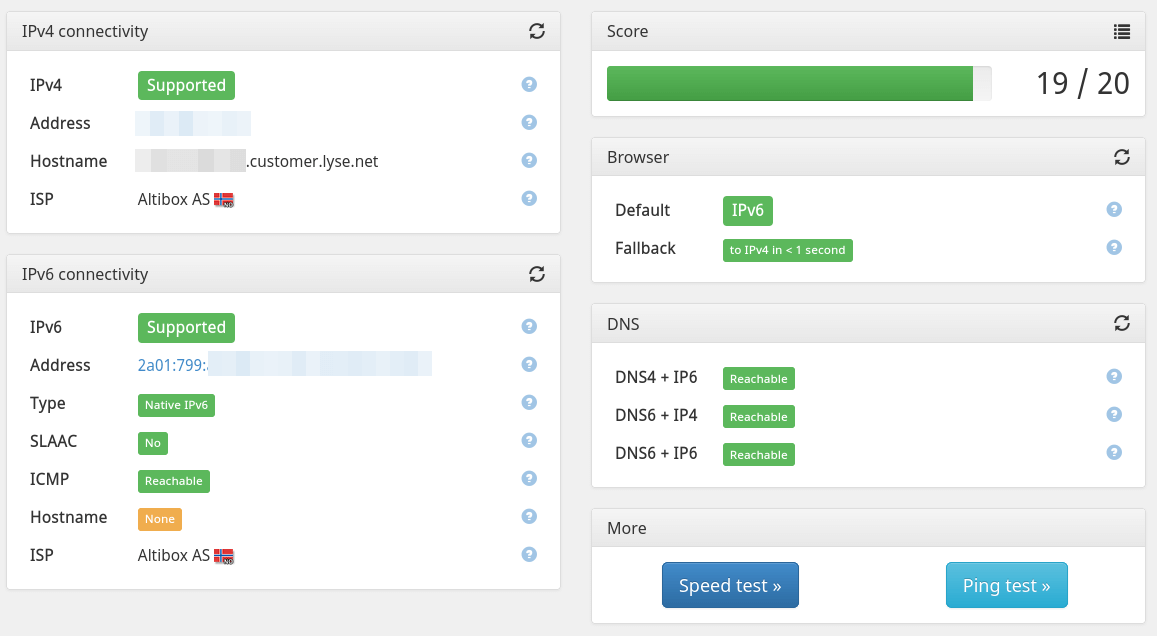
Success
After committing and saving the configuration changes, I navigated back to the EdgeRouter dashboard and found that my WAN and LAN interface now had IPv6 addresses! Success!
I did play a bit with different DHCPv6-PD settings and found that sometimes it just didn’t work. Not sure why.
After removing the entire DHCPv6-PD configuration and trying again; it worked. This happened on multiple occasions.
It could be that a reboot would have solved it, or that it just needed some time. But I was to impatient for wait for that 😛
What about router advertisement?
SLAAC requires Router Advertisement (RA) to work, but I hadn’t configured it… So why did it work?
A post on the Ubiquiti forum answered that:
When using SLAAC a Router Advertisement (RA) is definitely needed. But, with the EdgeRouter implementation an RA is created with the service slaac command within the WAN interface DHCPv6-PD context, so strictly speaking the RA configuration under the LAN interfaces is not needed. (…) — smf22
It goes on to talk about a file; /etc/radvd.conf:
hebron@ubnt:~$ cat /etc/radvd.conf
interface eth1 {
# This section was automatically generated by the Vyatta
# configuration sub-system. Do not edit it.
#
# service type [slaac]
#
IgnoreIfMissing on;
AdvSendAdvert on;
AdvManagedFlag off;
AdvOtherConfigFlag off;
prefix ::/64 {
AdvOnLink on;
AdvAutonomous on;
};
};
Aha! So the EdgeRouter as automatically configured router advertisement, with a /64 prefix on my eth1 interface. That’s why it’s working.
Closing remarks
I have only enabled IPv6 addresses on my LAN network, as this network doesn’t have any firewall restrictions to other networks. To enable it on DMZ, guest, IoT, etc; all firewall rules must be copied into the IPv6 firewall. This is important!
Last commit 2024-11-11, with message: Add lots of tags to posts.